Nmap & Zenmap
Zenmap is the official GUI version of nmap, a multi-platform network security scanner. (Windows, Linux, Mac OS X, etc). It is free and open source, easy for beginners and used by network and security professionals across the globe. Evaluating the security of your networks and systems is a must and can be done quite easily with this tool. To download Zenmap (packaged w/ nmap), find the user guide or check the man pages for reference, click the button below.
Scanning Networked Devices
After installation, be sure that the target devices are on and connected to the network. Once zenmap is open, locate the Target field and enter either the host name or IP address of the target machine to scan. Then locate the field named Profile and select the type of scan to perform. For this write-up we will be using the intense scan profile. Intense scans are very noisy and likely to be identified. However, are relatively quick and will provide a detailed overview of the target machine. Press Scan to initiate and select confirm if greeted with a UAC or User Account Control prompt (windows users).
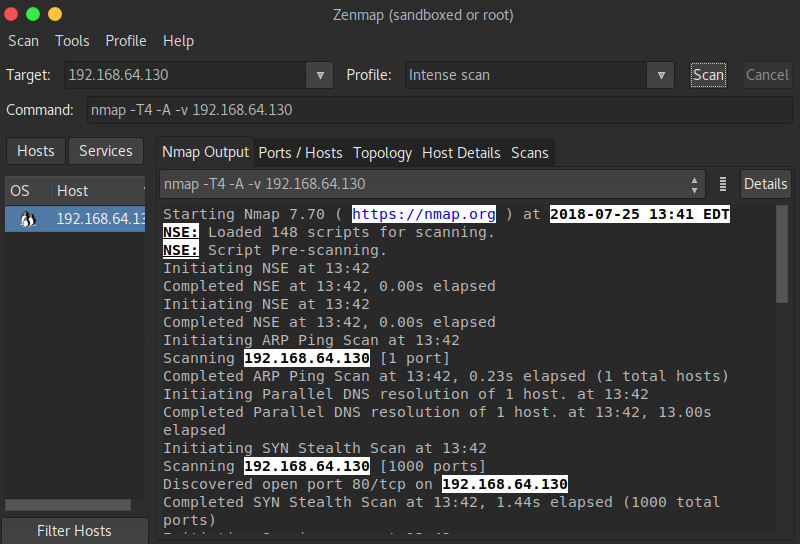
The output of the scan will return information about the target machine. Such as TCP & UDP Ports (open / closed), Hostname, Mac Address, and will even make a guess at what operating system the target is running. As a security professional, it is important to document nearly everything. Zenmap stores scans within a searchable database. Results can be saved, viewed, and used to compare against other scans.
The following tabs contain information crucial to a security researcher or penetration tester. Scan results can be used to harden the firewall protection for networked devices or even get past it!
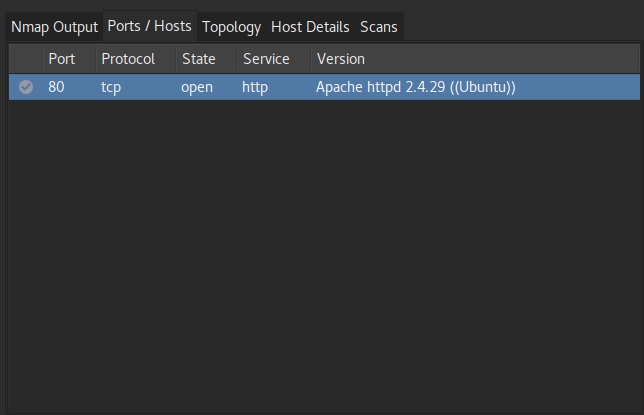
Ports/Hosts: Lists all open ports and what services are running on each. An attacker would use this information to check service versions against exploits to gain a foothold into the network.
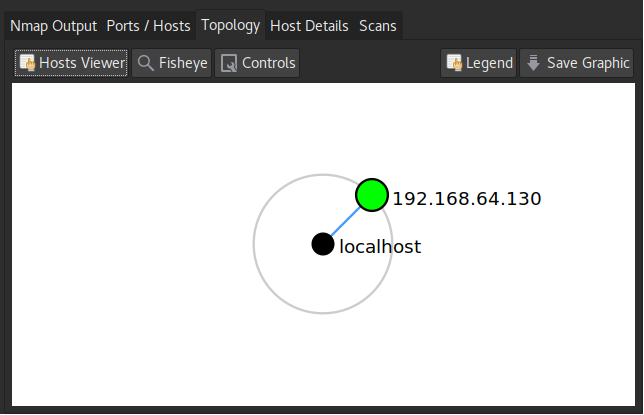
Topology: Shows where the device is positioned on the network relative to the position of the machine that made the scan.
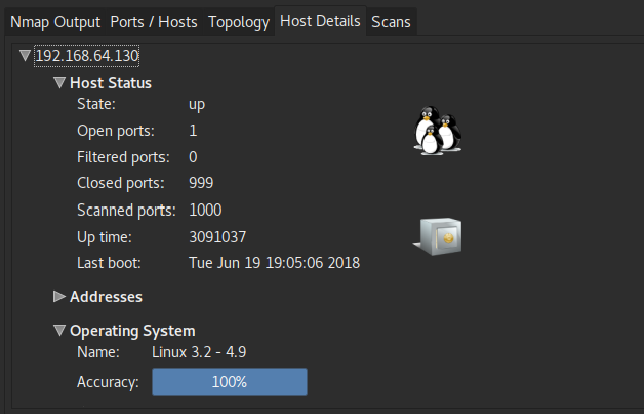
Host Details: This tab contains information such as the status of the host (up/down, ports scanned, up time, etc). Hostname and MAC address. Operating system the target is running. (In order for this to be done, at least one port must be open).
Overall we can see that Zenmap is a very powerful tool and easy to use. There are more advanced scanning techniques that can be used with this tool as well as a scripting engine NSE which allows for automation of networking tasks. (Very Handy!)
References & Guides
For more information regarding nmap, advanced scanning tecniques, cheat sheets, and using the nmap scripting engine. Follow the links below.
- SANS Institute – Nmap Cheap Sheet v1.0
- InfoSec Reference – Nmap Cheat Sheet
- Nmap From Beginner to Advanced
- Top 32 Nmap Commands for Linux Sys/Network Admins
- Using the Nmap Scripting Engine (NSE)
This tool will be used in future blog posts such as an upcoming penetration testing series. It is by far one of the most important tools to have in your kit.


